How GovCloud can help with your agency’s zero trust security journey

With the proliferation of ransomware attacks and data breach concerns, cybersecurity governance has become a top priority for agencies of all sizes. As per the Microsoft Digital Defense Report, the government is the most targeted sector by cybercriminals, accounting for 48% of all attacks from July 2020 to June 2021.
The need to better secure systems and data is driving more GovTech leaders to implement a zero trust security model along with a cloud strategy. When asked about government cybersecurity initiatives that will receive more attention in the next two to three years, 67% of the NASCIO’s 2021 State CIO Survey respondents cited the zero trust framework.
Key takeaways from this article include:
- Zero trust increases an organization’s security posture because it reinforces the need for continuous verification and threat detection.
- The White House is pushing agencies to adopt cloud technologies and the zero trust security architecture.
- GovCloud technologies can leverage zero trust implementations and enhance cybersecurity in the public sector.
What is the zero trust security model?
Zero trust is not a specific product. It is a security approach based on the assumption that no person or device should be trusted by default. All users and devices have to be continuously monitored to gain or maintain their network access.
The Department of Defense (DOD) Zero Trust Reference Architecture considers it “a dramatic paradigm shift in philosophy of how we secure our infrastructure, networks, and data, from verify once at the perimeter to continual verification of each user, device, application and transaction.” The core principle is to never trust, always verify.
Build a zero trust strategy to improve public sector cybersecurity
With a focus on strong identity identification, continuous monitoring, automation and segmentation, this cybersecurity framework seeks to prevent malicious actors from accessing critical assets. That’s why a zero trust policy can help build resilience in cybersecurity in the public sector. The strategy is to limit access only to resources and data that are needed, and then continuously look for anomalous or malicious activity. If a device is compromised, the damage is contained thanks to limited access privileges.
Deloitte lists zero trust among the key current technology trends in government, citing as benefits the opportunity for agencies to:
- Build a stronger security posture
- Simplify government cybersecurity management
- Enable modern IT practices
- Make better use of resources and automation
Establish cybersecurity governance best practices
For federal agencies, adopting the zero trust paradigm is no longer optional. In 2021, the Biden-Harris administration embraced this security model for the U.S. as part of the Executive Order on Improving the Nation’s Cybersecurity. The document calls for adopting a zero trust architecture and cloud-based technologies to improve network security.
Following up on the White House’s announcement, the Office of Management and Budget (OMB) released the draft of its Federal Zero Trust Strategy. The memorandum requires agencies to meet certain zero trust security goals by the end of the 2024 fiscal year. Measures include:
- Multi-factor authentication. That means that the user is only granted access after presenting more than one piece of evidence to verify identity. An example would be using a password together with a code sent to your phone.
- Device inventory. In order to protect all the assets in their network, agencies need to have complete visibility of all their devices.
- Increased encryption. Having the data encoded is critical to protect private and sensitive information from unauthorized access. If the data is encrypted, it remains hidden or inaccessible in case of a breach.
These requirements are directed to agencies at the federal level, but state and local governments can also benefit from moving toward zero trust security principles as part of their digital transformation initiatives.
How cloud technologies can improve government cybersecurity resilience
The U.S. Federal Zero Trust Strategy encourages the use of cybersecurity features present in cloud technologies. As noted in the Zero Trust Maturity Model by the Cybersecurity and Infrastructure Security Agency (CISA), legacy solutions may not support a zero trust approach.
The cloud can help enable a successful zero trust implementation because of its increased security controls. For example, cloud solutions have their own encryption and patching process in place. Amazon Web Services (AWS) already comes with standard features under zero trust principles. It’s even possible to limit access to sensitive information based on location, time and the individual.
Amazon highlights its approach to securing API requests as the “most prominent example” of Zero Trust principles at work within AWS. As the company explains, “Each one of these signed API requests is authenticated and authorized every single time at rates of millions upon millions of requests per second globally.”
GovTech services born in the AWS GovCloud
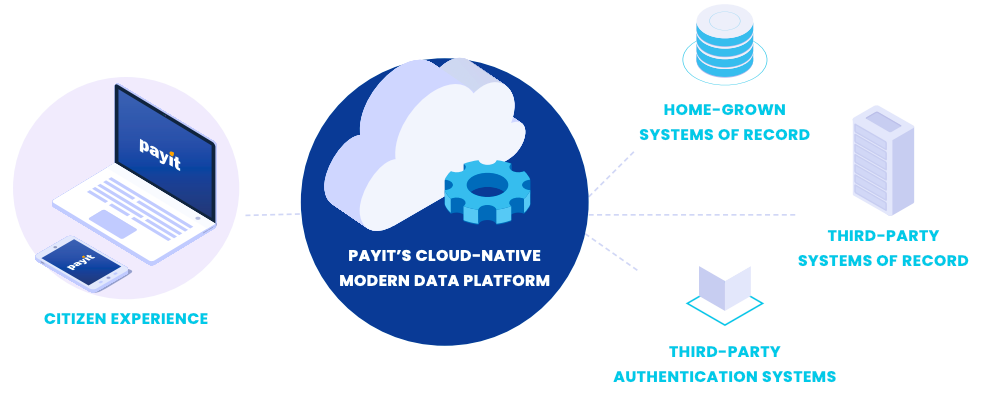
PayIt’s platform for digital services for government agencies is built natively in the AWS GovCloud.
Our cloud-native solution sits atop agency databases and consolidates government digital services and payments into one platform. This enables citizens to interact with different agencies through a single interface, bridging silos between departments. Our government software systems then communicate and update the necessary back-office systems for real-time transaction data and insights.
Our all-in-one government platform also allows citizens to use PayIt as their digital wallet app to securely store their documents, receipts and preferred payment methods online.
Government cloud platforms help meet compliance needs
GovCloud offerings differ from their commercial counterparts because they need to meet the unique regulatory requirements faced by government agencies. For example, there are federal rules governing how and where sensitive data is stored and who can access the data and network. With a GovCloud integration, agencies don’t need to meet those requirements on their own.
With PayIt’s SaaS platform, agencies can drive digital transformation in government while minimizing the security and compliance burden. Our government payments solution complies with:
- Federal Risk and Authorization Management Program (FedRAMP) cybersecurity standards
- DOJ Criminal Justice Information Systems (CJIS) Security Policy
- DOD Cloud Computing Security Requirements Guide (SRG) for Impact Levels 2, 4 and 5
PayIt’s smart government solutions take further security measures to protect citizens’ and agencies’ data and transactions. For example, the PayIt platform:
- Provides strong encryption to protect data from unauthorized access
- Is PCI Level 1 Merchant certified, offering an extra layer of protection against credit card frauds
- Uses tokenized payments to secure citizens’ banking details during transactions
Enable a secure digital government transformation with PayIt
Take the first step toward improved cyber resilience in government by booking a PayIt demo and learning how our cloud-based platform keeps government and citizen data secure.
Looking for more content?
Get articles and insights from our monthly newsletter.